How to decrypt TLS Sessions of browsers like Chrome and Firefox without Man-in-the-Middle MitM/Adversary-in-the-Middle AitM (Att&ck T1557) like ARP Cache Poisoning, DNS Spoofing, LLMNR/NBT-NS Poisoning and SMB Relay, DHCP Spoofing, Proxy, burp, PAC, WPAD, etc:
This is a silent way to debug issues. However your EDR/SIEM/logings solution should check for SSLKEYLOGFILE entries in your environment variables because this is a silent way to break TLS without informing the user.
Use the SSLKEYLOGFILE in your environmentvariables of your windows, linux or macos system.
Windows
Simply create an environmentvariable called SSLKEYLOGFILE and set the value of the path to the text-file, in which the TLS private keys should be saved:
Linux
Simply create an environmentvariable called SSLKEYLOGFILE and set the
value of the path to the text-file, in which the TLS private keys should
be saved:
export SSLKEYLOGFILE=$HOME/tlsprivatekeys.txt
export SSLKEYLOGFILE=$HOME/tlsprivatekeys.txt
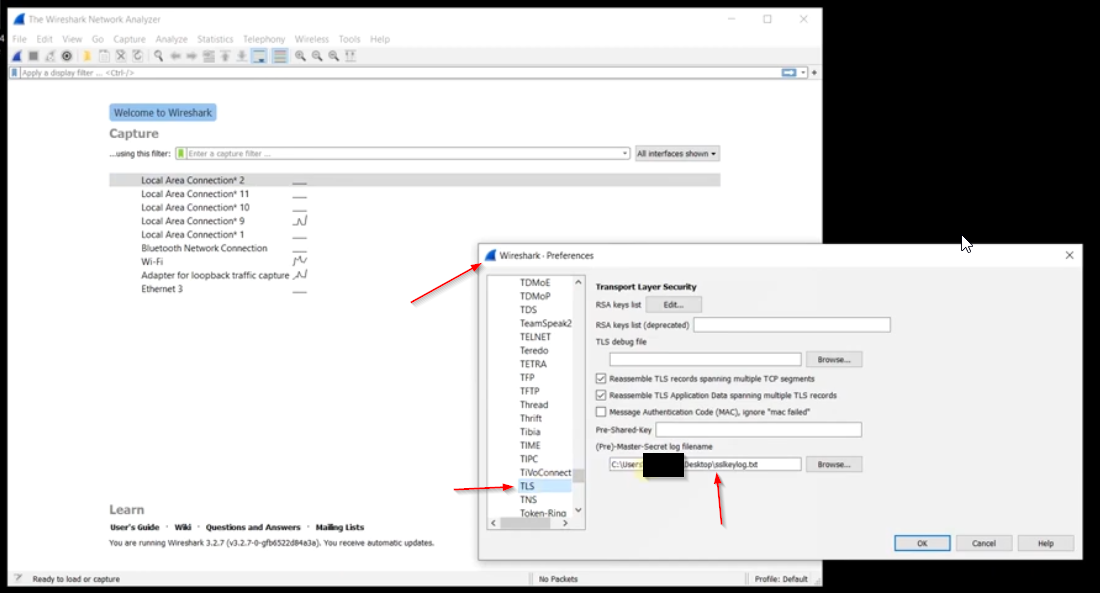
Decrypt TLS sessions with Wireshark
- Open the wireshark prefecenses
- Go to TLS
- Select your SSLKEYLOGFILE text file as (Pre)-Master-Secret filename as shown in the following screenshot: