Pepe Berba has created a nice overview of linux persistence techniques as a map: https://pberba.github.io/security/2021/11/22/linux-threat-hunting-for-persistence-sysmon-auditd-webshell/
Linux persistence techniques as a map
eBPF will change a lot like JavaScript did - Netflix example
Netflix released an article about how they use eBPF in order to track and analyze network application traffic without having issues with ressources as well as without having to load extra kernel modules, which almost always break, when the next kernel update is installed.
In my opinion eBPF will change a lot like JavaScript did, not only network analysis, but also for security products (like advanced endpoint protection, antivirus, forensic tools, etc), for interface extensions, monitoring systems and so on.
Netflix article about how they use eBPF: https://netflixtechblog.com/how-netflix-uses-ebpf-flow-logs-at-scale-for-network-insight-e3ea997dca96?gi=669388aa6aa6
SIEM Use Case - find suspicious powershell commands
Microsofts Powershell is a very mighty tool, which can be used as LoLBin. To detect suspicious powershell commands or scripts, a SIEM use case in order to find suspicious powershell-commands can be:
Logging / Data Source
Active PowerShell Script Block Logging (Event ID 4104) OR use your Advanced Endpoint Protection AEP or Endpoint Detection and Response EDR tool like VMware Carbon Black, Microsoft Defender ATP, Crowdstrike or the other tools.
SIEM use case / fetch suspicious powershell
1. process = powershell.exe
&&
2. cmd = ToBase64String OR FromBase64String OR -e OR -en OR -enc OR -enco OR -encod OR -encode OR -encoded OR -encodedc OR -encodedco OR -encodedcom OR -encodedcomm OR -encodedcomma OR -encodedcomman OR -encodedcommand OR -ec
&&
3. not cmd = Windows\CCM\*
More very useful information
- https://attack.mitre.org/techniques/T1059/001/
- https://www.splunk.com/en_us/blog/security/hellsbells-lets-hunt-powershells.html
- https://www.carbonblack.com/blog/decoding-malicious-powershell-streams/
- https://blog.talosintelligence.com/2019/11/hunting-for-lolbins.html
- https://devblogs.microsoft.com/powershell/powershell-the-blue-team/
- https://www.fireeye.com/blog/threat-research/2016/02/greater_visibilityt.html
- https://github.com/redcanaryco/atomic-red-team
Real world examples of attack chains with Att&ck mapping
Parinacota attack chain

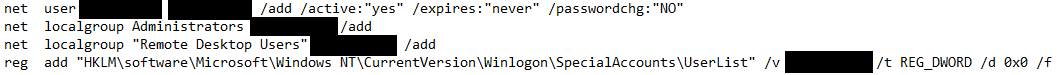
The article on Parinacota includes details like how for example persistence is archived:
- Windows Registry modifications using .bat or .reg files to allow RDP connections

- Setting up access through existing remote assistance apps or installing a backdoor
- Creating new local accounts and adding them to the local administrators group
Wadhrama attack chain
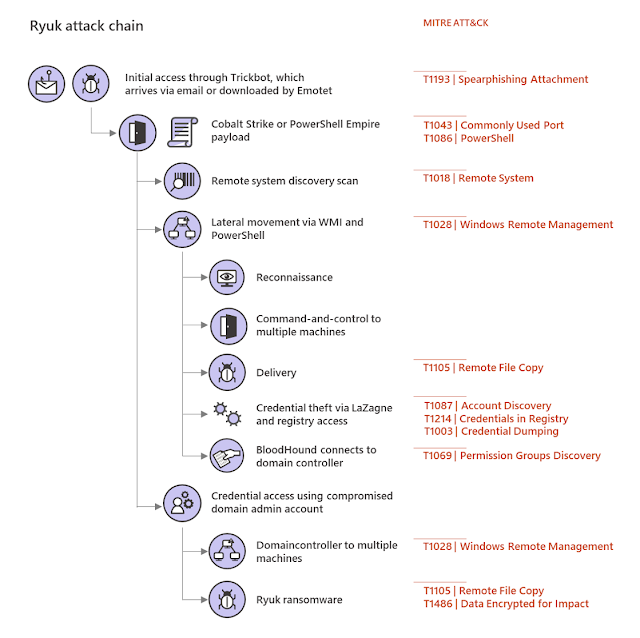
Ryuk attack chain
Doppelpaymer attack chain
How to increase IT security of a company using quick wins
- Implement Multi-Factor-Auth or 2FA. Trying to balance security with comfort will let you win your users, for example by implementing MFA or 2FA using PushTokens.
- Raising awareness by regularly sending internal phishing mails will make them learn and understand, not to open or click on everything.
- Implementing zero trust or microsegmentation will make lateral movement hard.
- Regularly scanning your whole environment for vulnerabilities and configurations issues with regular patching and improving hardening will dramatically reduce your attack surface.
- Restrict administrative permissions, regularly checking if they are still necessary, implementing JIT and securing your directory services using special jump servers with MFA/2FA will help further. Also don't use Microsofts AD Built-in default groups because very often the have to many unnecessary permissions
Some more are described in an article from Microsoft security blog. I personally don't agree on all of them, but it is a possible approach:
Example of Spear Phishing Attack in detail
SIEM IoC regsvr32.exe outbound network connection
A starting point can be searching your SIEM logs for network connections from regsvr32.exe to a not RFC1918 private ip address and your IPv6 address space.
Mitigations could be using the Windows firewall to block outbound network connections from regsvr32.exe or as MITRE Att&ck writes:
"Microsoft's Enhanced Mitigation Experience Toolkit (EMET) Attack Surface Reduction (ASR) feature can be used to block regsvr32.exe from being used to bypass whitelisting. Identify and block potentially malicious software executed through regsvr32 functionality by using application whitelisting tools, like Windows Defender Application Control, AppLocker, or Software Restriction Policies where appropriate."
More useful searches for Splunk & Sysmon environments can be found on Github, example: https://github.com/mitre-attack/car/issues/11 and testing if your AEP/EDR/Sysmon or log-collection-tool actually logs regsvr32 events is described here: https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/T1117/T1117.md
Advanced Endpoint Protection Testing from MITRE using ATT&CK
Round 1 Testing
In round 1 the following AEP/EDR products were tested:
The following vendors/products will follow:
- Cyberreason
- F-Secure Countercept
- Fireeye Endpoint Security
- McAfee MVision
- Palo Alto WildFire Traps XDR
Example
As an example you can look at the results of the Microsoft Windows Defender ATP results. You can see all techniques which were tested and how the product worked. You even can see screenshots of it:
Screenshot of Microsoft Defender ATP of MITRE ATT&CK Evaluation Round1 Testing 1.A.1 User Execution T1204:
Summary
This is amazing work done by MITRE! 👍 It provides transparency of the Advanced Endpoint Protection AEP/Endpoint Detection and Response EDR products, lets you compare them, check which techniques they protect against and how they work in terms of forensics.Round2 is already running. 👌
Monitor UniFi WLAN Access Point with PRTG with SNMPv3 Auth+Encrypted
This is a tiny guide howto monitor your UniFi wireless accesspoint, in this case a Unifi U7 pro with SNMPv3 with AES-Encryption and SHA-Auth...

-
You can either use the GUI of the FortiGate to list all certificates, or use the CLI. Either using the commands: Using the "get...
-
If you are running a Windows Server 2016, are using the integrated Windows Server Backup utility and you want to save the backup to a remote...
-
Howto add a route with a specific interface into the windows routing-table. This can be useful for example if you have a tunnel-all vpn...